MailSlurp API access requires an API key in the header. This guide focuses on secure setup patterns, not just copy-paste examples.
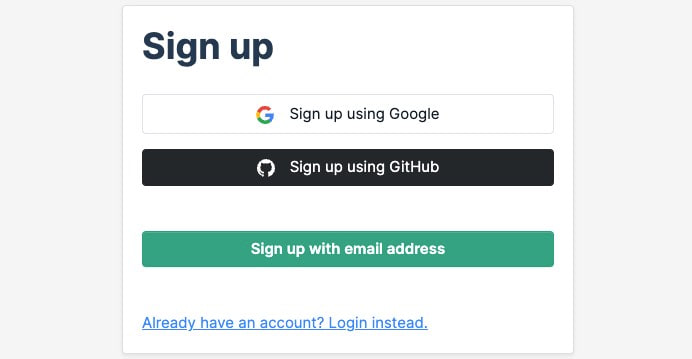
1) Create or access your account
Sign up or log in:
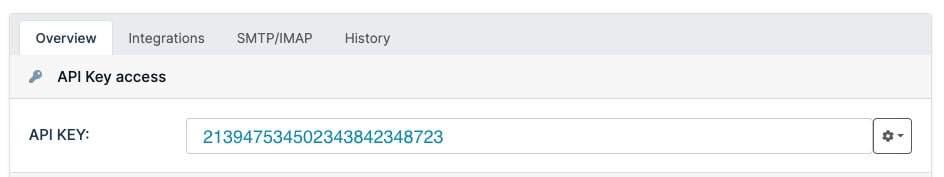
2) Find your API key
After login, open the dashboard and copy your key from the API section.
3) Store keys by environment
Do not hardcode keys in source files.
Recommended layout:
- local development: shell environment variable
- CI: secret store (GitHub Actions, CircleCI contexts, etc.)
- production services: cloud secret manager + rotation policy
4) Use the key in HTTP requests
If you receive or , first verify key source and environment injection.
5) Configure SDK clients
Most SDKs use the same header under the hood.
Node.js example:
More SDK references: developer docs.
Security checklist
- rotate keys on a schedule and after team changes
- keep separate keys for local, CI, and production systems
- scope usage per service where possible
- redact keys from logs and error messages
- audit old or unused keys regularly
Common mistakes
Using the wrong header name
Use (not unless a specific SDK layer requires it).
Checking keys into git
If a key is exposed, rotate it immediately and clean affected history where necessary.
Sharing one key across all systems
Split keys by environment so revocation and incident handling are safer.

