Videos
Check out our tutorial video series.
Deliver emails with confidence using MailSlurp's email verification API. Validate addresses in code or through the online dashboard for improved deliverability.

Sending emails is a common requirement for many modern applications and enterprises. Use MailSlurp's free email API to validate email addresses in code or using an online dashboard. See the developer email validation documentation for more details.
A bounced email is an email that is returned to the sender by a receiving mailserver that refused or could not process the message. This typically occurs when sending emails to addresses that do not exist or are full. When a mailserver returns many emails to a sender the sender is considered a bad actor and their spam ranking is marked down. Therefore it is important to reduce the bounce rate when sending emails.

When sending emails with Mailslurp a is used that servers can send a bounce back to. When they do MailSlurp records a bounce event against your account. There is a maximum daily bounce rate and a maximum total bounce count that limits your account. Exceeding these limits can result in temporary account freeze.
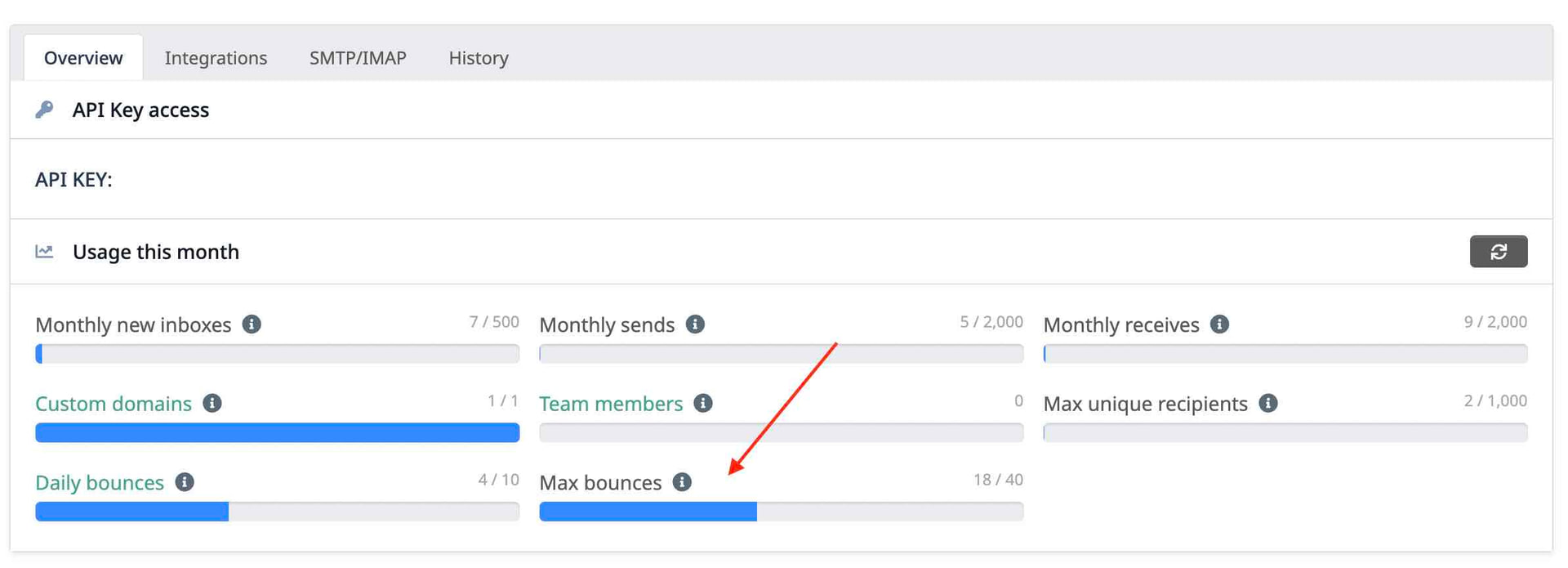
If your account is temporarily frozen due to exceeding maximum bounce count please contact support to re-enable your account or upgrade to a plan that allows email verification
Click the sidebar link to view your account bounces:
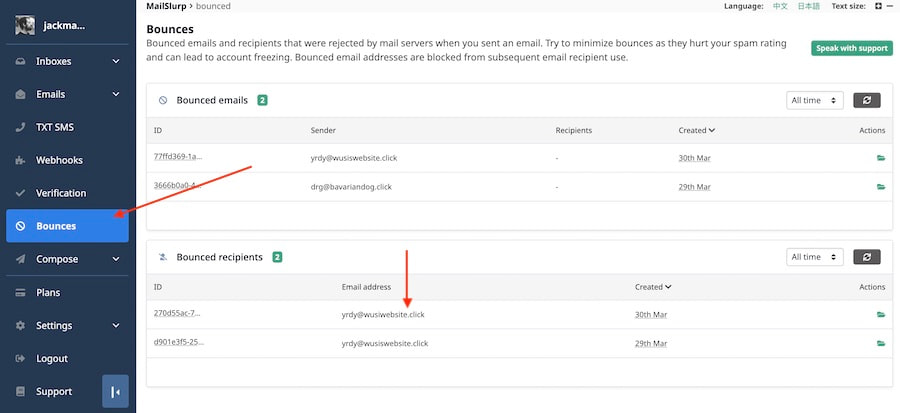
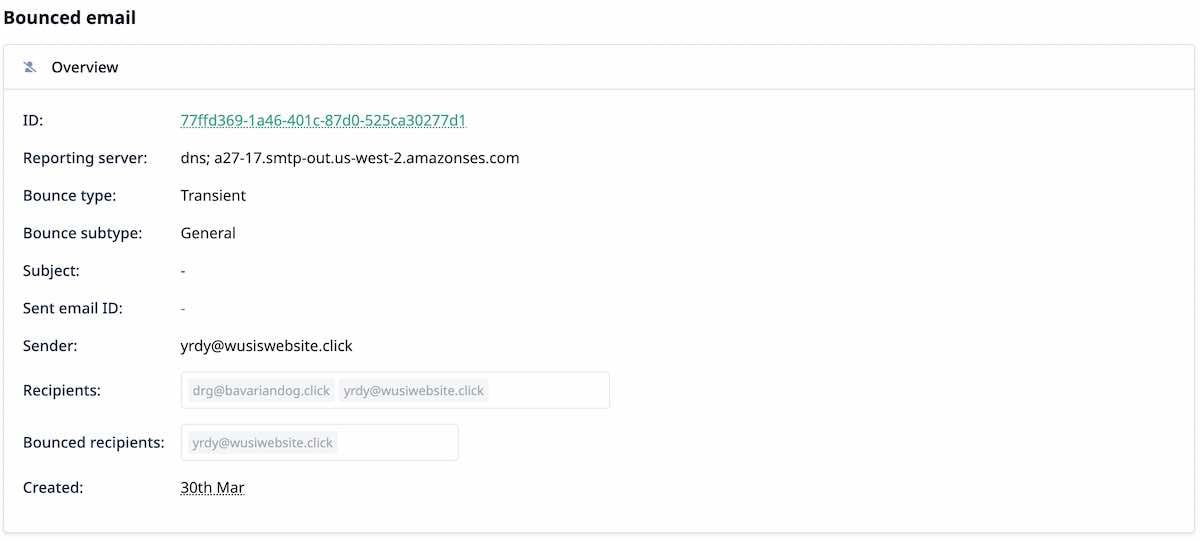
Click on a bounce to view the bounce message and diagnose the cause of the rejection. Try to prevent sending to similar addresses or use the validation features to filter out bad email addresses when sending.
If you are writing an email application in Csharp, Javascript, Ruby, Python or any other language you probably want to check email addresses before sending emails. This reduces the risk of sending an email to an address that does not exist. Emailing non-existing email addresses can result in bounce warnings or SMTP complaints. Complaints and bounces affect your sending reputation and email delivery rate. To avoid improve your email sending validate, verify, or check your email recipients before sending.
Too many bounces or complaints from emails sent from your account can lead to sending ability being suspended. If this happens please contact support.
When sending marketing emails in MailSlurp use the sending validaiton options in the compose screen to verify email addresses during sending using the MailSlurp web app dashboard.
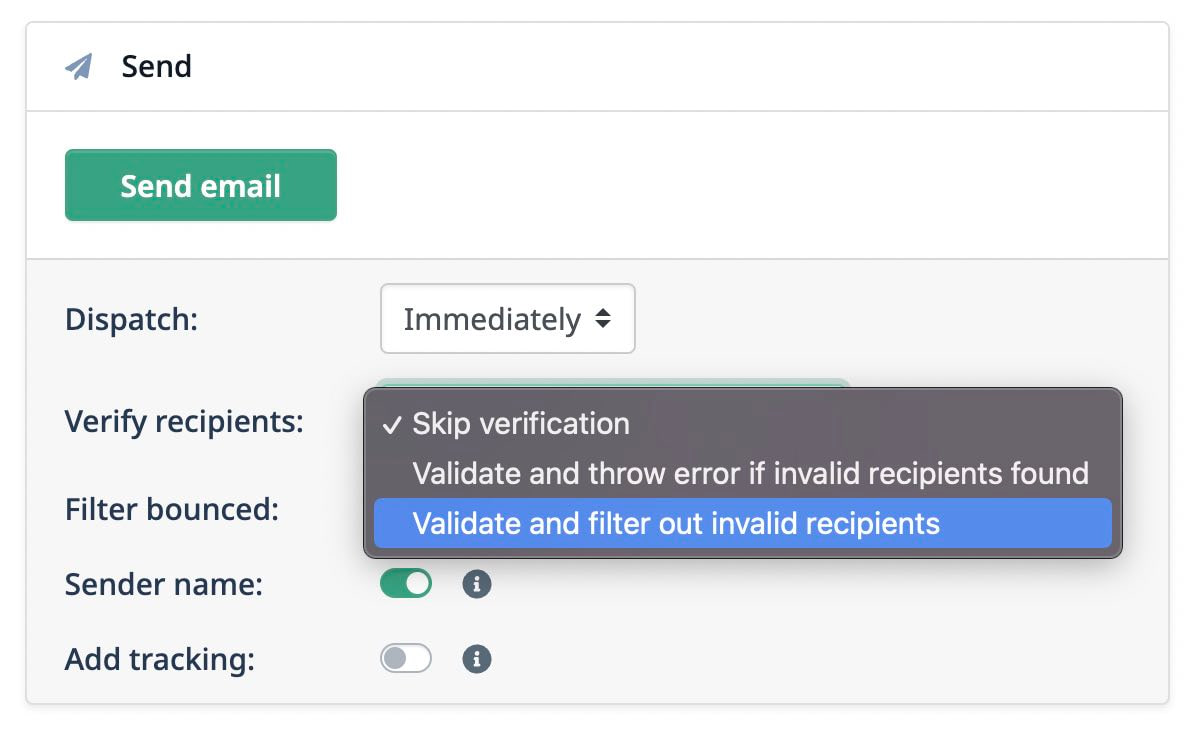
You can also enable filtered of any previously bounced recipients with the check-button below:
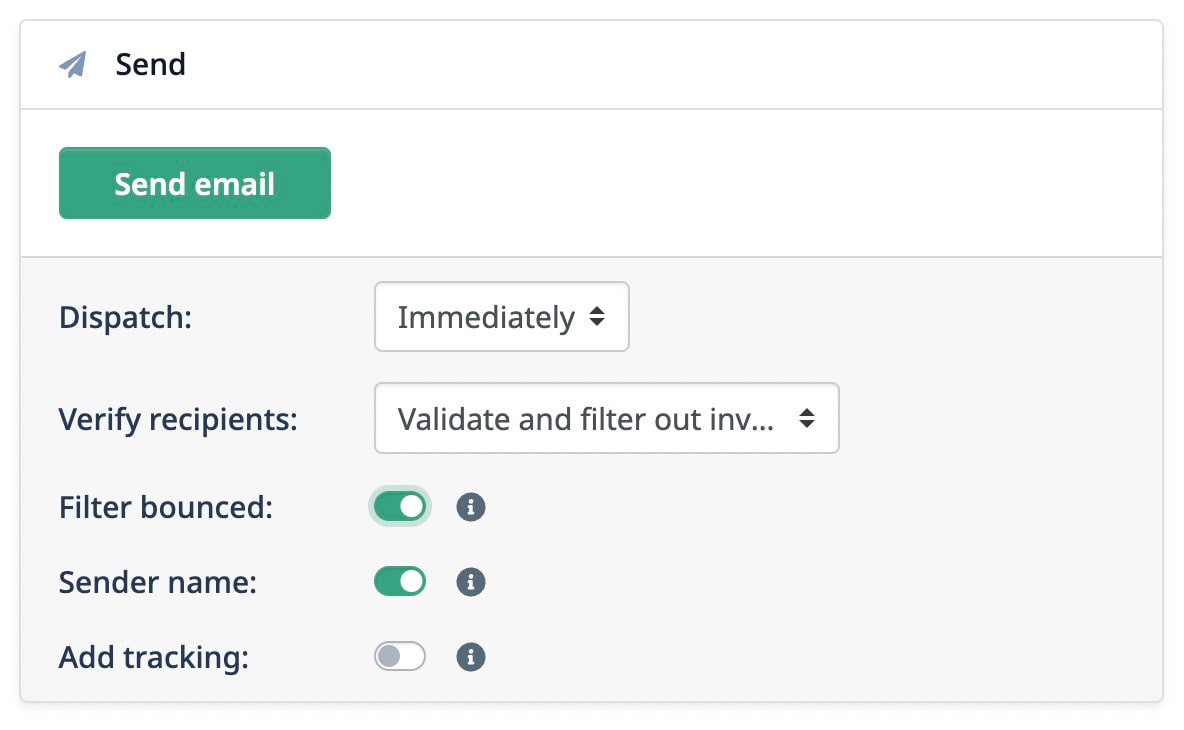
Filtering bounced emails will ensure no emails are sent to any addreses that caused a bounce in your account in the past.
When you want to check a list of email addresses to see if they exist use the EmailVerificationControllerAPI client in a language of your choice. Verifying email addresses in Javascript is easy:
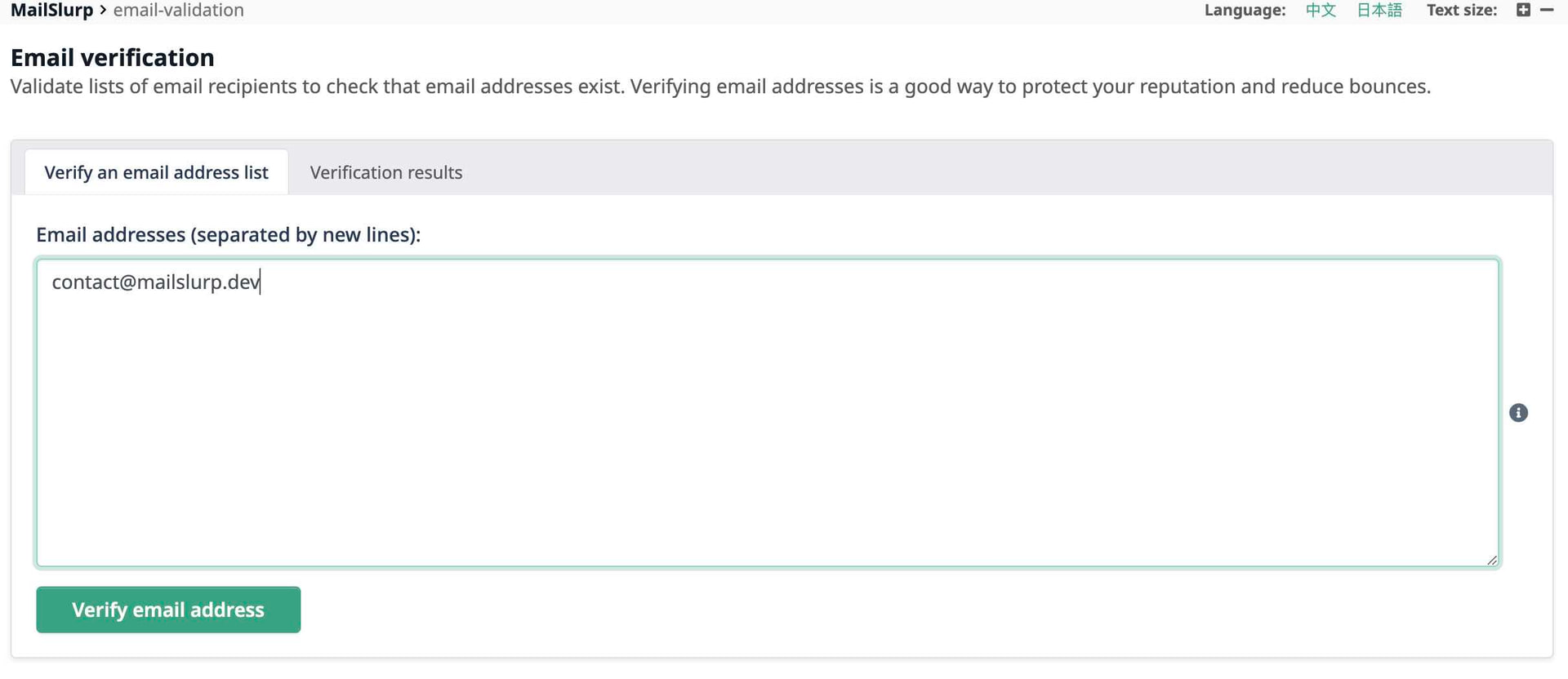
You can also verify emails in the dashboard and view the results online.
Combine MailSlurp's powerful email checking algorithms and live SMTP mailserver checks to filter invalid recipients from your emails when sending. See the following email sending example in Java:
MailSlurp offers a powerful online dashboard for validating email address and contact lists in bulk. Simple sign up and navigate to the verification section. Enter your addresses separated by a new line and click verify to check each address against remote mail servers to see if they exist and accept mail.
The best way to avoid additional bounces is by creating an account webhook for and events. See the webhook documentation for event descriptions.
With webhooks your server is sent a payload each time a bounce occurs containing the email addresses of bounce recipients. You can save these bounced email addresses to a ban list and avoid sending to them in the future. See the account webhook guide for more information.
A raw multipart MIME message delivered with SMTP can contain multiple parts with different headers.
Email messages are Mime Message format that is often multi-part. The parts of the SMTP message body are marked with Content-Type headers. RFC6522 describes the delivery of administrator messages. These admin content parts are used to transmit a delivery status notification or undelivered email when a bounce occurs. When the message is returned to the MailSlurp server a header such as below is sought:
Bounce emails returned to the sender normally contain a standard content part with a message about delivery.
Then after that will sometimes be a content part with headers in the body that indicate the reporting mail transfer agent (Reporting MTA) and a diagnostic message for the final recipient.
RFC3464 describes the delivery status content part that is included by most mail transfer agents when a bounce is returned to the :
The original undelivered message is included in the returned email.
You can view and diagnose bounce alert in your account on the bounces page of the app.
Check out our tutorial video series.
Email and SMS guides for automation and testing.
View github project code for multiple languages.
Latest posts from the MailSlurp team.
Test, build, and automate messaging with a free MailSlurp account.