Videos
Check out our tutorial video series.
Mastering Multi-Factor Authentication: A Guide to Implementation and One-time Passwords" - A comprehensive guide to secure and user-friendly MFA.
Multi-factor authentication (MFA) is used to add an extra layer of security to your systems and network. It is used to verify the identity of a user before granting him access to the application or system he is trying to log into. How a certain website verifies a user's identity? It does so by asking the user several authentication questions that only you should know. For example, if you are logging into your online bank account, before allowing you to get in and perform actions, the application asks you for a code that is sent to your mobile device via email. After entering that code, you are granted access to your bank account. In this article, you will learn everything about MFA and how to implement it successfully. So, let's begin:
The authentication factor refers to the category that a website uses to verify a user. MFA is categorized into three authentication factors: Knowledge (something you know such as PIN, username, or password), possession (something you have such as a mobile or credit card), and inheritance (something you are such as your fingerprint scan, facial recognition, retina scan, or biometric data). For successful implementation of MFA, your business needs to employ a minimum of two of these categories.
When an application sends an authentication code to a user's mobile device via email or SMS message, that code is known as one-time password (OTP). OTP consists of a pseudo-randomly generated password that is valid for only a few minutes and then expires after that short time to preserve the security of a system and prevent any mishap. So, even if a user recycles the same password for many accounts, the confidentiality of his data is secured by OTP that is uniquely paired with each username and password. There are multiple ways to deliver OTP to user's devices:
SMS (Short Message Service) is a widely used service for sending OTP to users. After typing the username and password of the account, users receive a text message containing the OTP which is entered and sent back to the application. Though this method is very user-friendly but, it is not advised to use anymore due to its vulnerability.
Email is another way to deliver OTP to users which they can copy and enter into the required space. Unfortunately, email is also not a safe alternative since the password of the email and the application that is requiring the OTP can be same due to the wide recycling of passwords for multiple accounts. And, it's not difficult for hackers to steal or guess passwords.
Authenticator app is a third alternative to receive OTP on a user's cell phone. All a user needs to do is install the app and create his all accounts that are supported by the app to receive the OTPs which are regenerated every 30 seconds so you don't need to depend on any email or text. Just open the app and you will find the OTP there. The most popular examples of authenticator apps are Duo, Authy, and Google Authenticator.
Many users abstain from using MFA to avoid multiple steps to sign into their account or application because of the slow user experience. But, security is also a critical requirement to maintain. So, how to balance between security and user experience? Step-up authentication plays a significant role to enhance the user experience as well as security by allowing applications to authenticate with a stronger mechanism in order to gain access to sensitive resources.
MFA can be easily implemented in your apps. Discussed below is an example of how you can run MFA in few minutes using Auth0.
Enter the code in the text box and click on continue. Then, you will be asked to copy a recovery code which will be helpful to you in case you lose your phone. Click on 'Continue'. You will be directed back to the application, and you are successfully signed in. This way, MFA will put an additional layer of security on your account, keeping your data more secure and confidential.
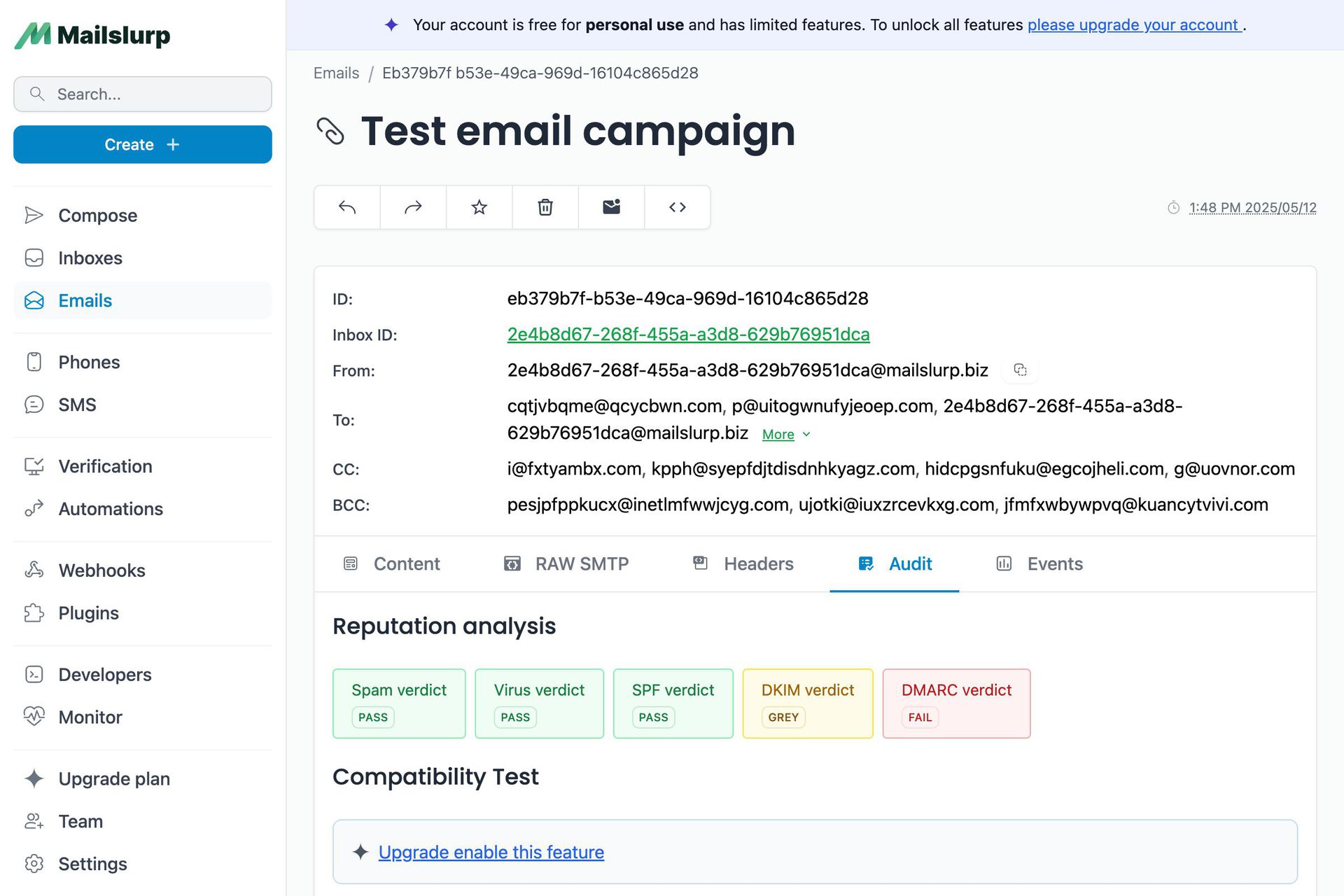
If you use Auth0 or similar SSO/MFA services it is important to test your integration using real phone numbers and email addresses. MailSlurp provides an extensive MFA testing tool for verifying SMS and email verification codes.
Check out our tutorial video series.
Email and SMS guides for automation and testing.
View github project code for multiple languages.
Latest posts from the MailSlurp team.
Test, build, and automate messaging with a free MailSlurp account.