Videos
Check out our tutorial video series.
Configure identity providers like Okta to enable enterprise SSO login to shared email accounts. Create company mailboxes with auto-forwarding and RBAC login.

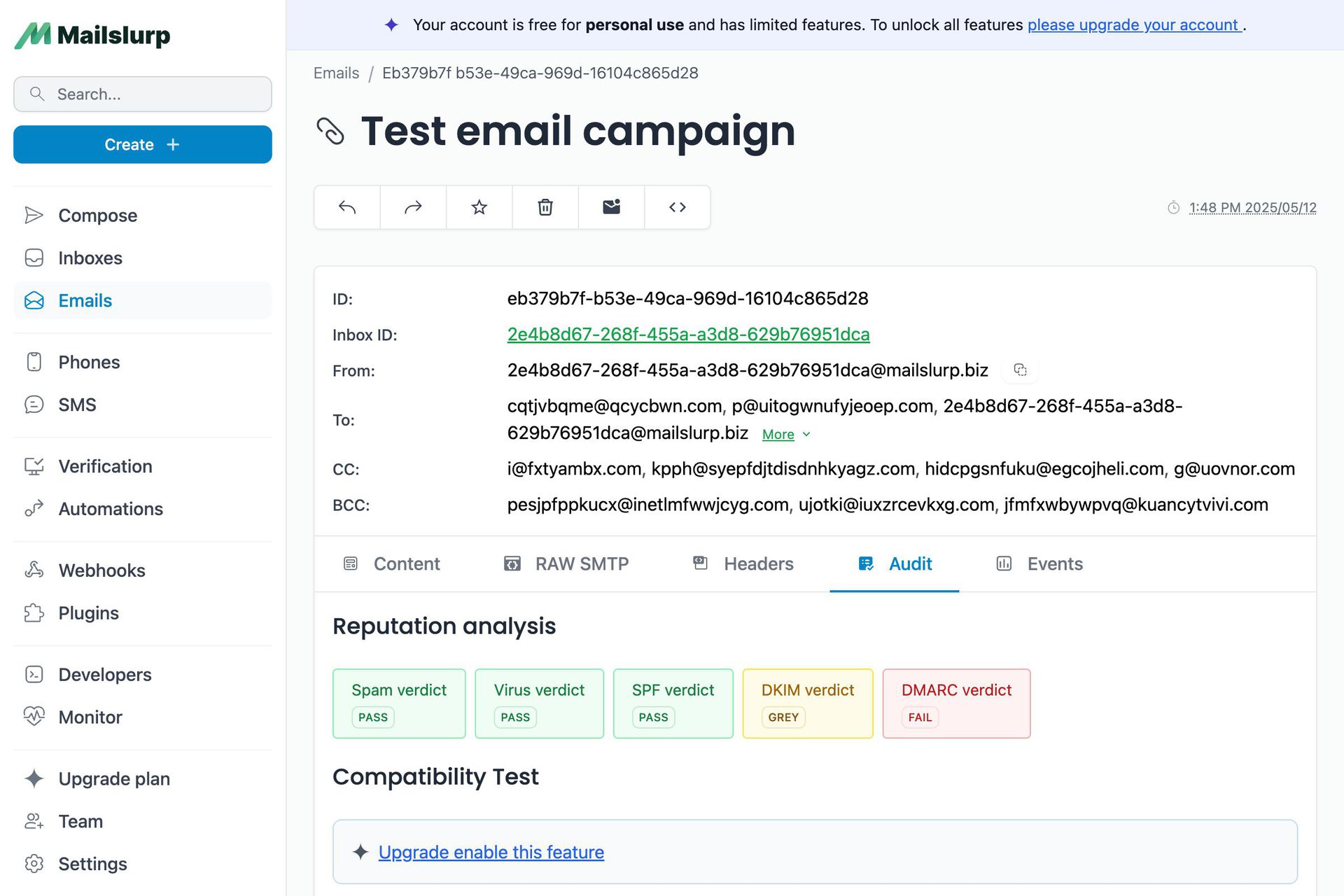
MailSlurp enterprise plans support SSO SAML login. This post will demonstrate how to establish an integration with your Okta identity pool. While these steps apply to Okta they also apply to other identity providers that support SSO. This guide assumes you have created a MailSlurp organization in the dashboard app.
Log into your Okta or IdP account and create a new internal application pairing using SAML 2.0:

Specify SAML 2.0 for the sign in method:

Add a name and application icon if desired.

An important step is to provide your Idp with an ACS SAML assertion URL so that you can login. For the Audience URI use the same ACS URL.

Use the slug for your organization instead of the
slug shown in the images.
You must tell your IdP to map the email address of your user to the name ID so that MailSlurp can identify them. For name ID format use . For application username use .
Next view the setup instructions for your SAML integration:
The SAML settings can be found in Okta by click the button on the Okta integration page.

Click the view setup button to reveal the X.509 certificate, issuer, and sign on URL.

Copy these values into the MailSlurp SSO settings form on the organization page:

Save the SAML settings to enable the MailSlurp integration.
Invite and manage users using your identity provider. Users can access the application at , the enterprise homescreen , or using the IdP access page.

Check out our tutorial video series.
Email and SMS guides for automation and testing.
View github project code for multiple languages.
Latest posts from the MailSlurp team.
Test, build, and automate messaging with a free MailSlurp account.