MailSlurp enterprise account plans support single sign-on using the SAML protocol. You can configure your corporate identity provider (such as Okta) to connect users with the MailSlurp dashboard application.
Common provider integrations
Please see the guides below for integrations with common providers.
- Configure Okta SAML login with MailSlurp
- Configure Ping Identity SAML
Step-by-step guide
Enabling single sign on in MailSlurp requires an external identity provider and an enterprise MailSlurp subscription.
1) Create a MailSlurp account
First you must create a MailSlurp account.
2) Upgrade to an Enterprise account
Then upgrade to an enterprise plan to enable teams.
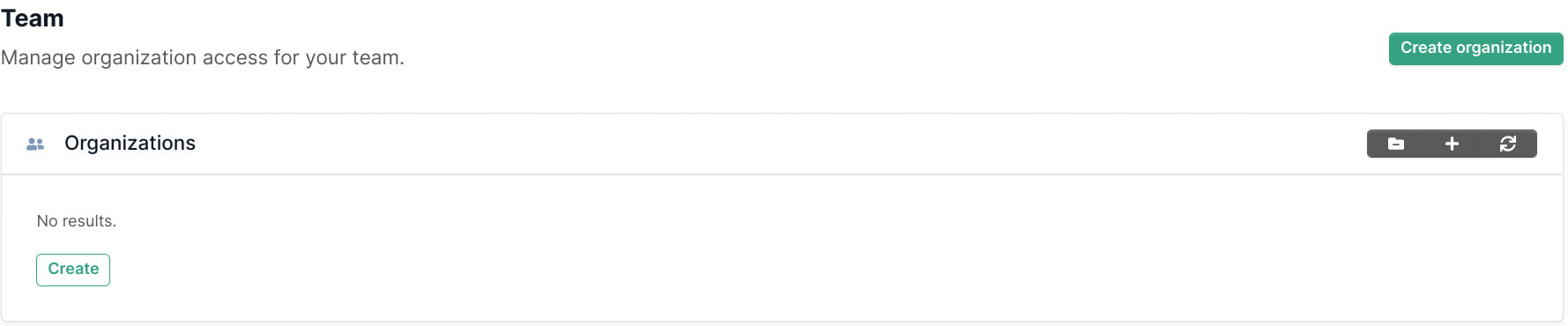
3) Create an organization in MailSlurp
MailSlurp organizations allow team access to inboxes with access several roles.
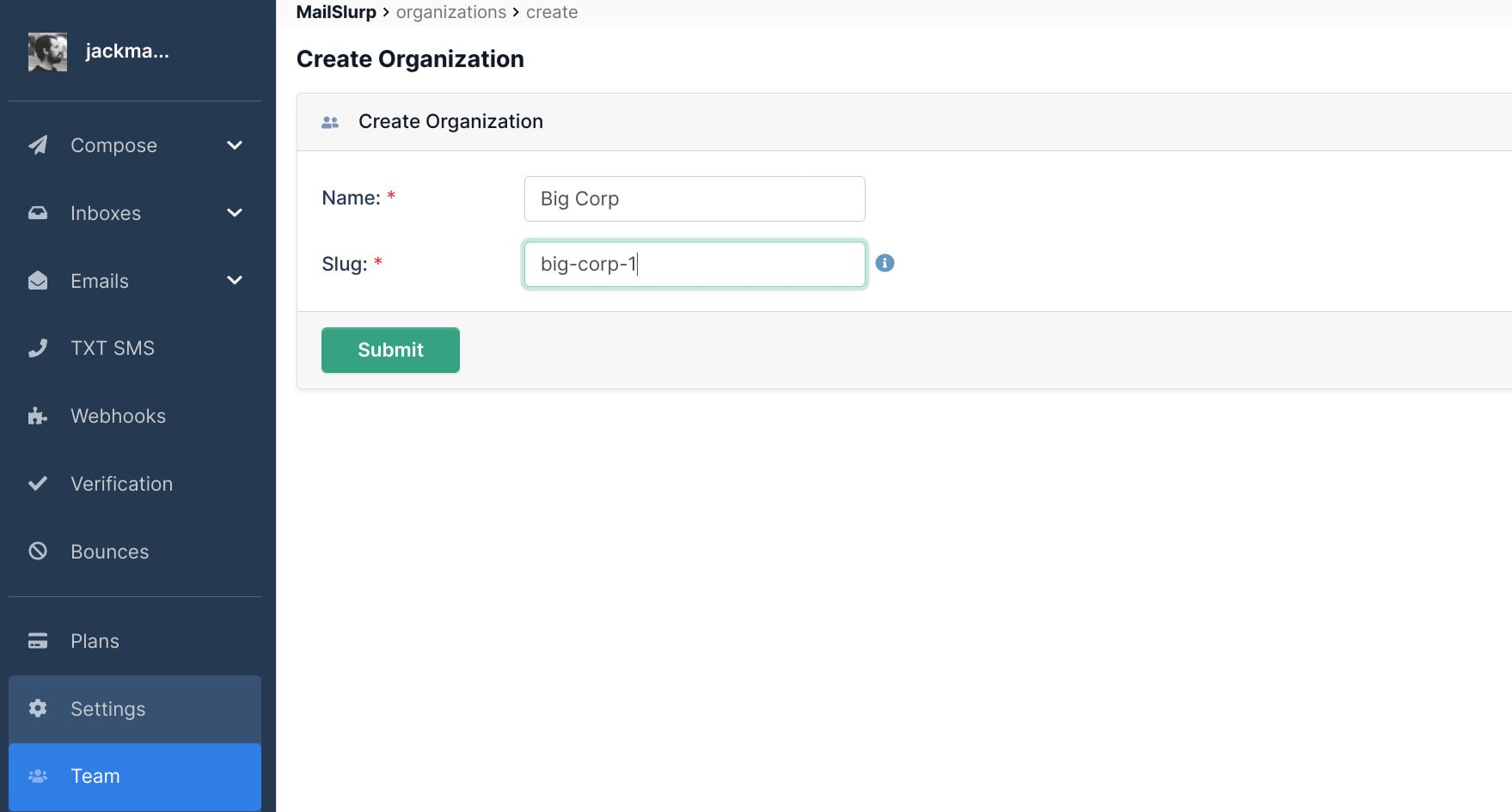
Create an organization by clicking in the sidebar. Add your organization name and slug then click save.
The organization
is a unique identifier for your integration
4) Click configure SAML settings
On the organization page click to create a SAML connection.
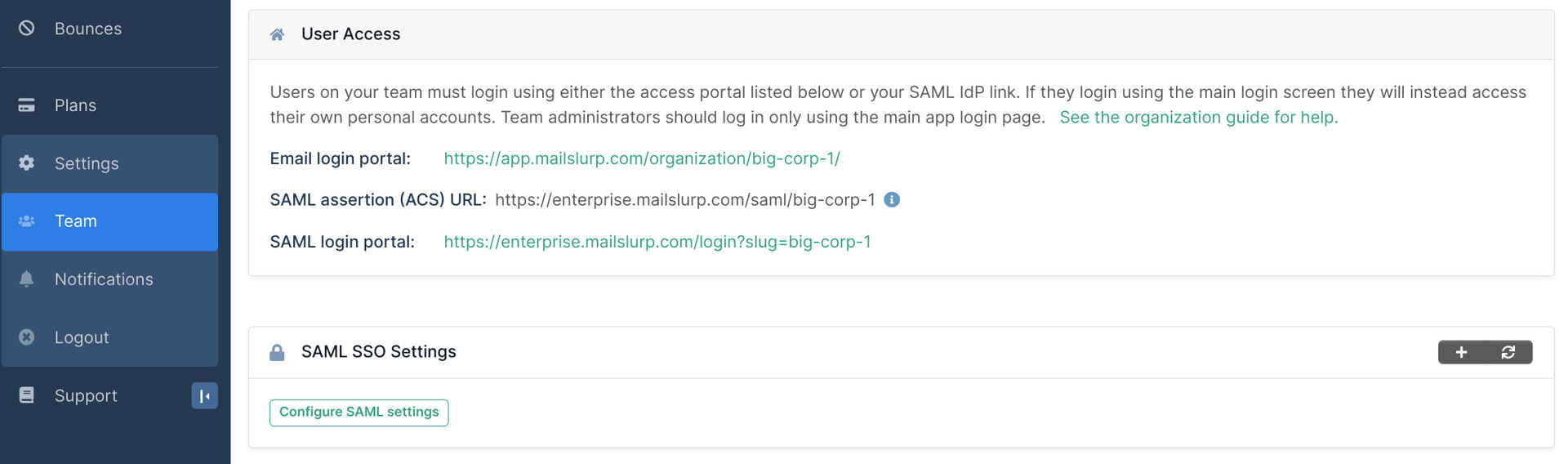
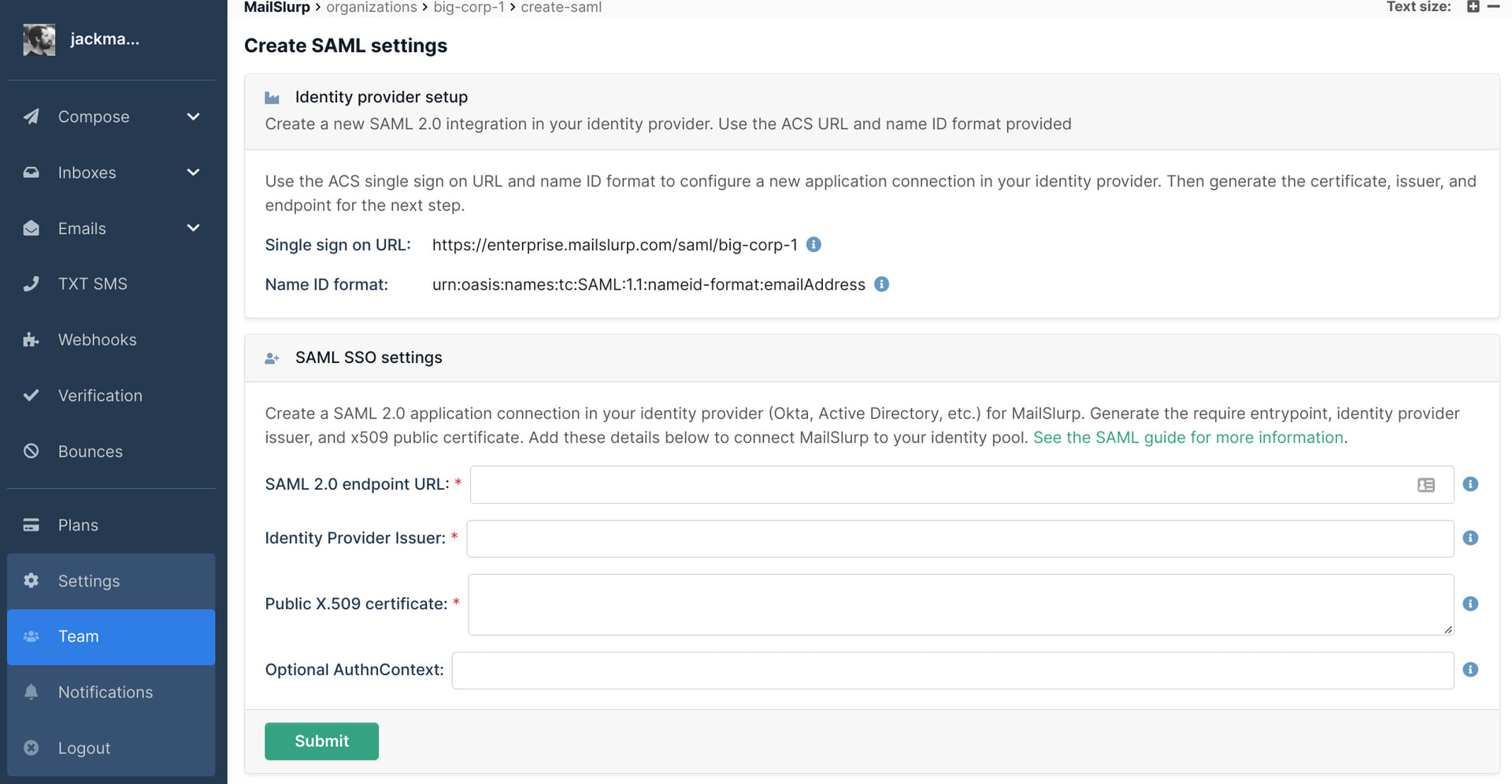
The SAML settings page provides the MailSlurp service provider ACS URL, the audience URI, and the name format. Copy these values into your IDP application integration.
5) Copy identity provider setup to your Idp
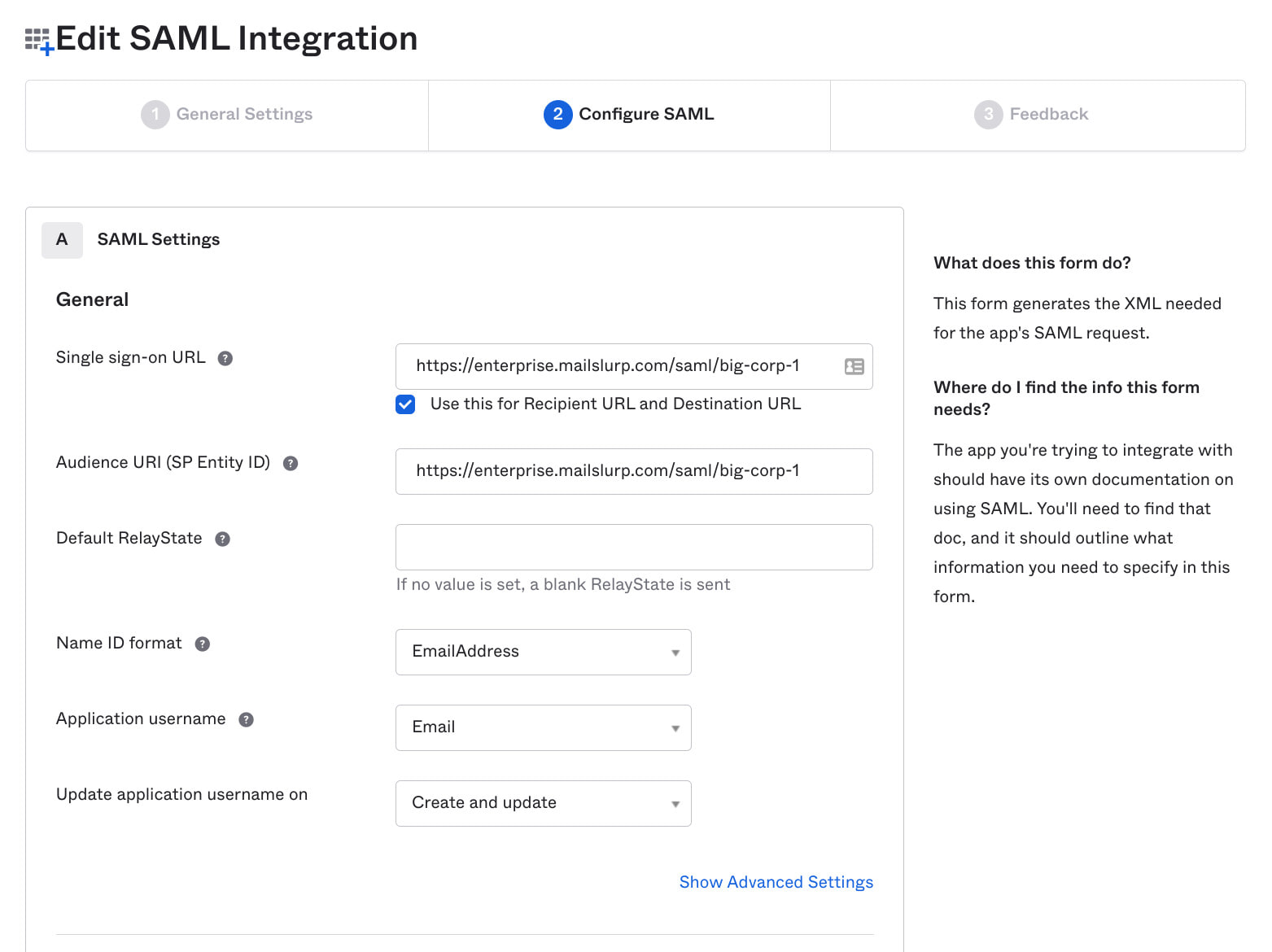
Open you identity provider and create a new SAML application integration.
- Add the SSO URL (ACS):
- Use same value for audience SP-ID:
- For name ID format use
Save the integration in your Idp. In Okta this looks like so:
6) Copy Idp integration details into MailSlurp SAML SSO settings
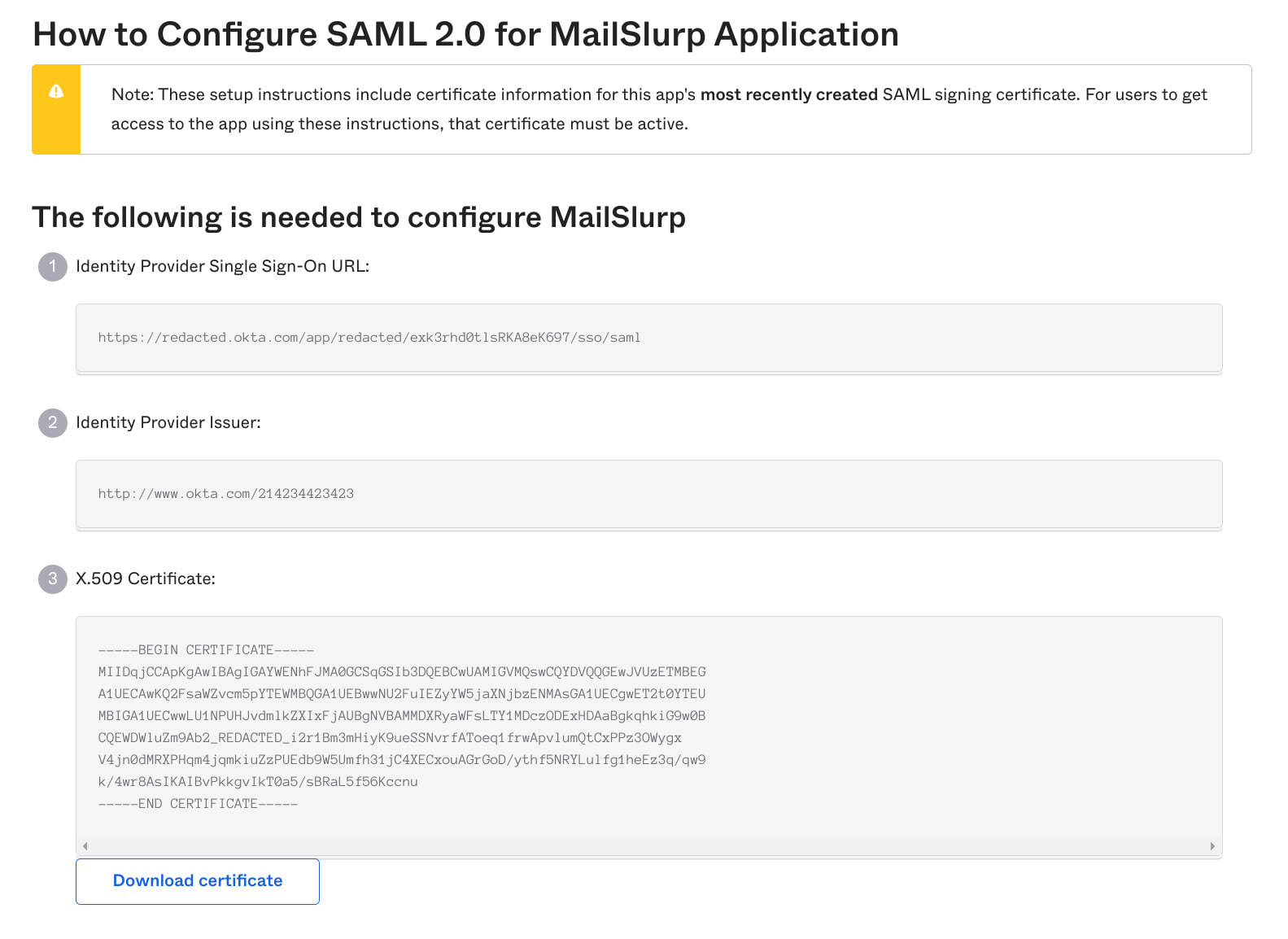
Once you add the application to your identity provider you must copy the SAML endpoint, issuer and X509 certificate into the MailSlurp SSO settings panel so that MailSlurp can connect to your Idp integration.
- Fill the SAML endpoint URL in MailSlurp
- Fill the identity provider issuer
- Add the X.509 certificate
If you are using Okta you can find these details by clicking the button:
Save the SAML SSO settings in MailSlurp in the form.
7) Direct users to login page
Once your SAML settings are saved you can direct your organization users to login via the enterprise portal

